ICS/SCADA
Penetration
Testing Toolkit
Web-based GUI for scanning, reading, writing and attacking industrial control systems. Built for authorized security testing, CTF competitions, and ICS security research.
Web-based GUI for scanning, reading, writing and attacking industrial control systems. Built for authorized security testing, CTF competitions, and ICS security research.
Full-featured web interface — scan, read, write, and attack industrial protocols from your browser.
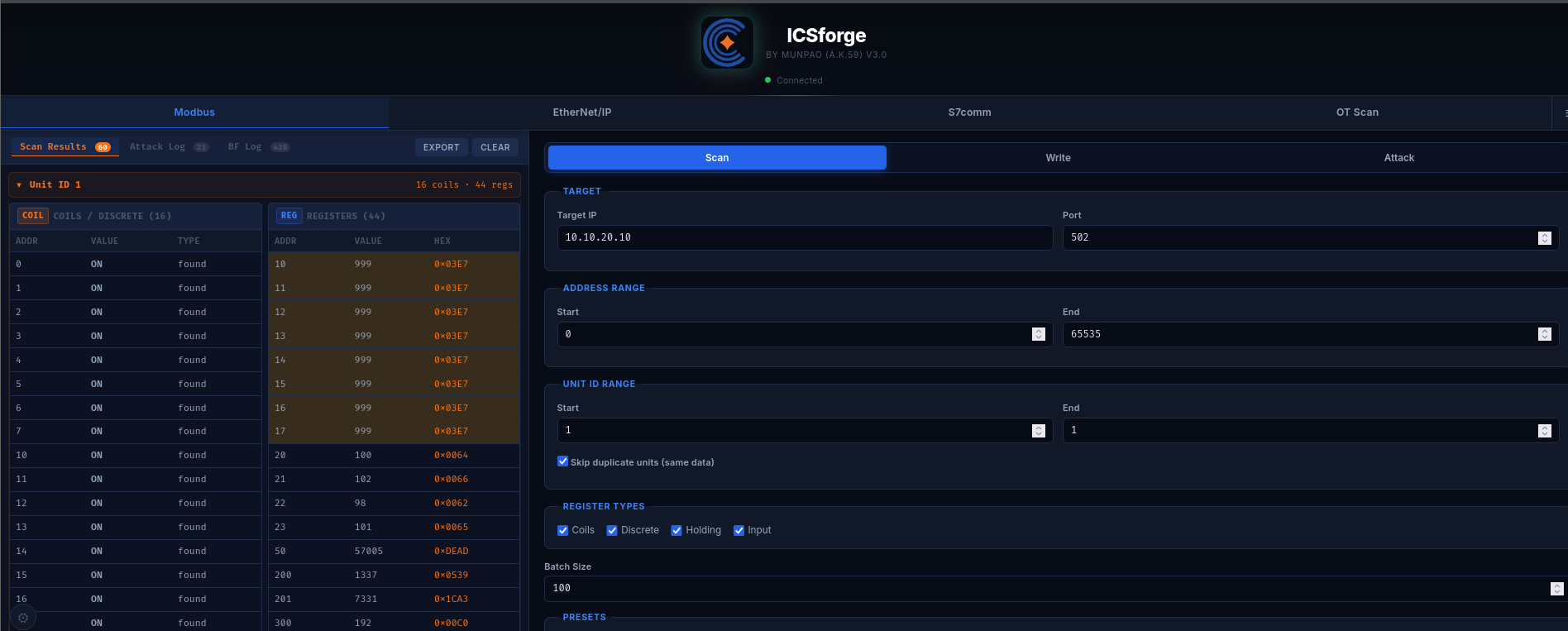
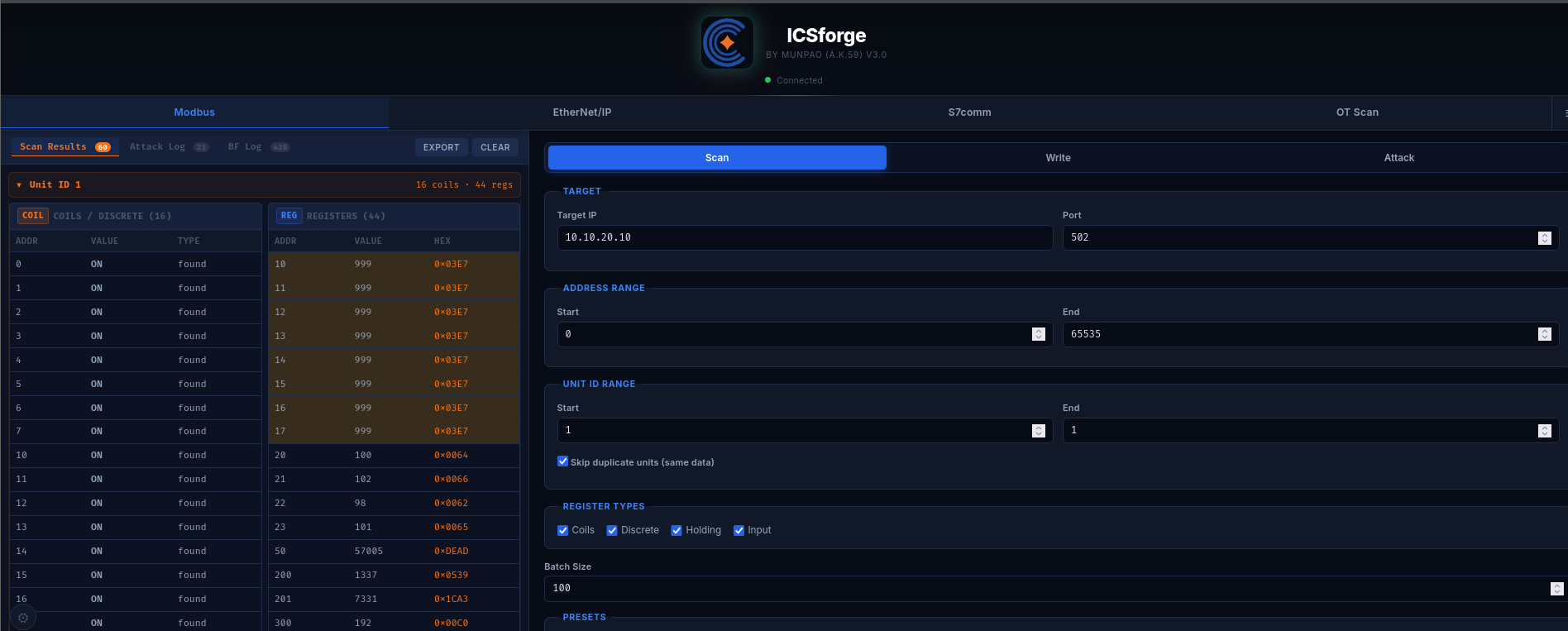
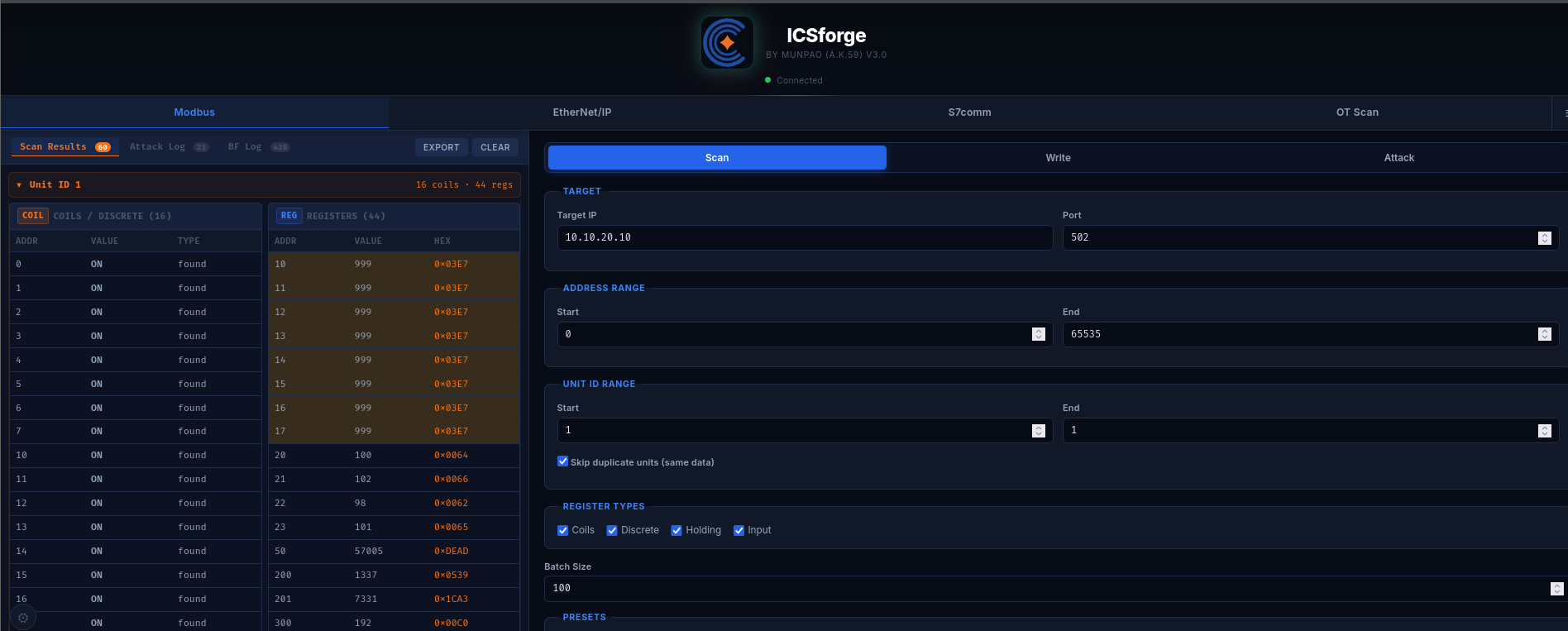
ICSforge is a web-based ICS/SCADA penetration testing toolkit built for security professionals, CTF competitors, and industrial cybersecurity researchers.
It provides a unified GUI for interacting with industrial protocols — Modbus/TCP, EtherNet/IP CIP, and S7comm — with features ranging from basic scanning to advanced attack simulation.
Complete feature matrix across all supported industrial protocols.
| Feature | Description | Impact |
|---|---|---|
| Scan (FC01-FC04) | Coil/register scan with secret detection | RECON |
| Write Coil (FC05) | Force output ON/OFF, trigger shutdowns | HIGH |
| Write Register (FC06) | Modify setpoints, thresholds | HIGH |
| Auth Bypass | Fuzz auth registers with preset payloads | HIGH |
| Value Bruteforce | Write payloads across address range | MED |
| Race Condition | Burst write with value cycling | HIGH |
| Crash Test | Malformed PDU fuzzing | HIGH |
| Feature | Description | Impact |
|---|---|---|
| Scan | ListIdentity + tag enumeration | RECON |
| Read/Write Tags | Tag read/write via pycomm3 | HIGH |
| Auth Bypass | Tag-based auth fuzzing | HIGH |
| Tag Bruteforce | Value bruteforce across tags | HIGH |
| Race Condition | Burst write with value cycling | HIGH |
| Feature | Description | Impact |
|---|---|---|
| Scan | CPU info + firmware via SZL | RECON |
| DB Read/Write | Data block operations | HIGH |
| CPU STOP | Send PLC stop command | HIGH |
| Memory Fuzzer | Write fuzz values to DB | HIGH |
| Replay Attack | Replay captured S7 PDU hex | HIGH |
| Protocol | Port | Detection | Info |
|---|---|---|---|
| Modbus/TCP | 502 | FC43 Device ID | Vendor, firmware, unit IDs |
| EtherNet/IP | 44818 | ListIdentity | Device type, serial |
| S7comm | 102 | COTP + SZL | CPU type, firmware |
| DNP3 | 20000 | Data link probe | Device address |
| BACnet | 47808 | Who-Is broadcast | Device ID, vendor |
No separate install step — dependencies auto-install on first run.
Free and open source. Use in your lab, CTF competitions, or authorized assessments.